-
 4 most important files SSH connections | TechRepublic
4 most important files SSH connections | TechRepublic
-
 Delete SSH Authorized Keys from Linux -
Delete SSH Authorized Keys from Linux -
-
 Known Hosts –
Known Hosts –
-
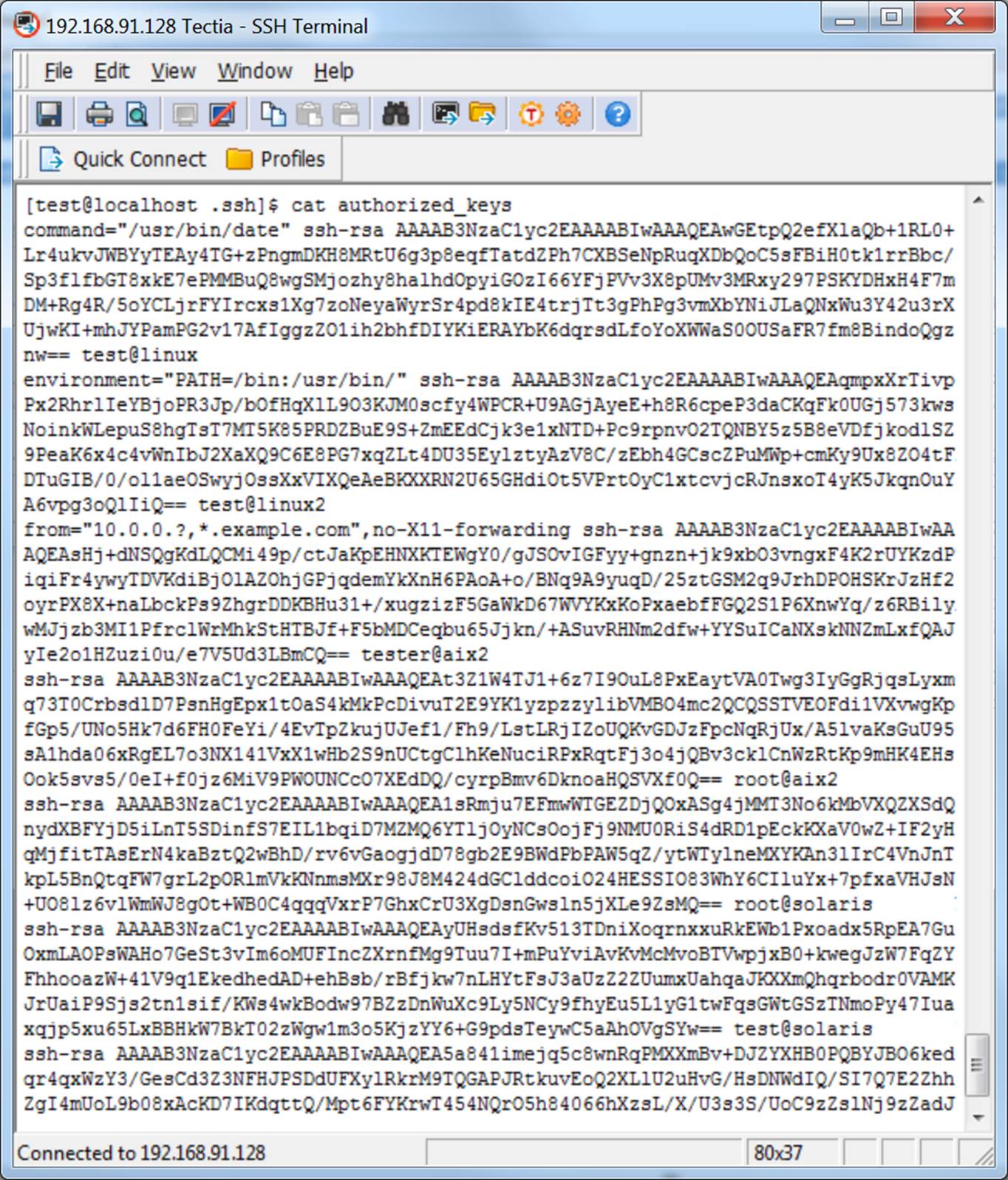
 Restrict login using SSH keys to particular IP address - Experiencing Technology
Restrict login using SSH keys to particular IP address - Experiencing Technology
-
 Known_hosts.yml headaches - Roots Discourse
Known_hosts.yml headaches - Roots Discourse
-
 How Configure SSH Authentication on a Linux Server
How Configure SSH Authentication on a Linux Server
-
 networking - Can't ssh even with public key added to authorized_keys - Ask
networking - Can't ssh even with public key added to authorized_keys - Ask
-
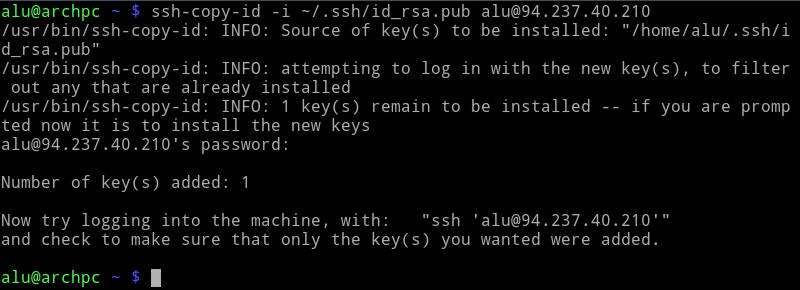
 Setting Up SFTP Key Authentication On The Command Line | JSCAPE
Setting Up SFTP Key Authentication On The Command Line | JSCAPE
-
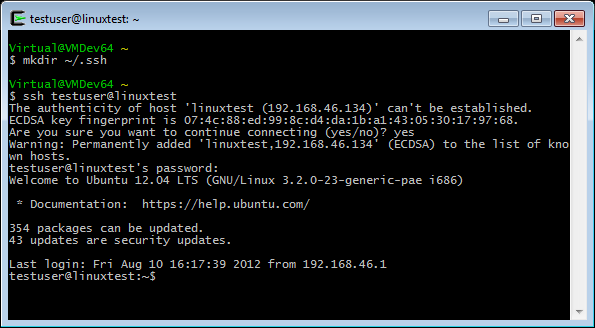 SSH public key authentication – VisualGDB Tutorials
SSH public key authentication – VisualGDB Tutorials
-
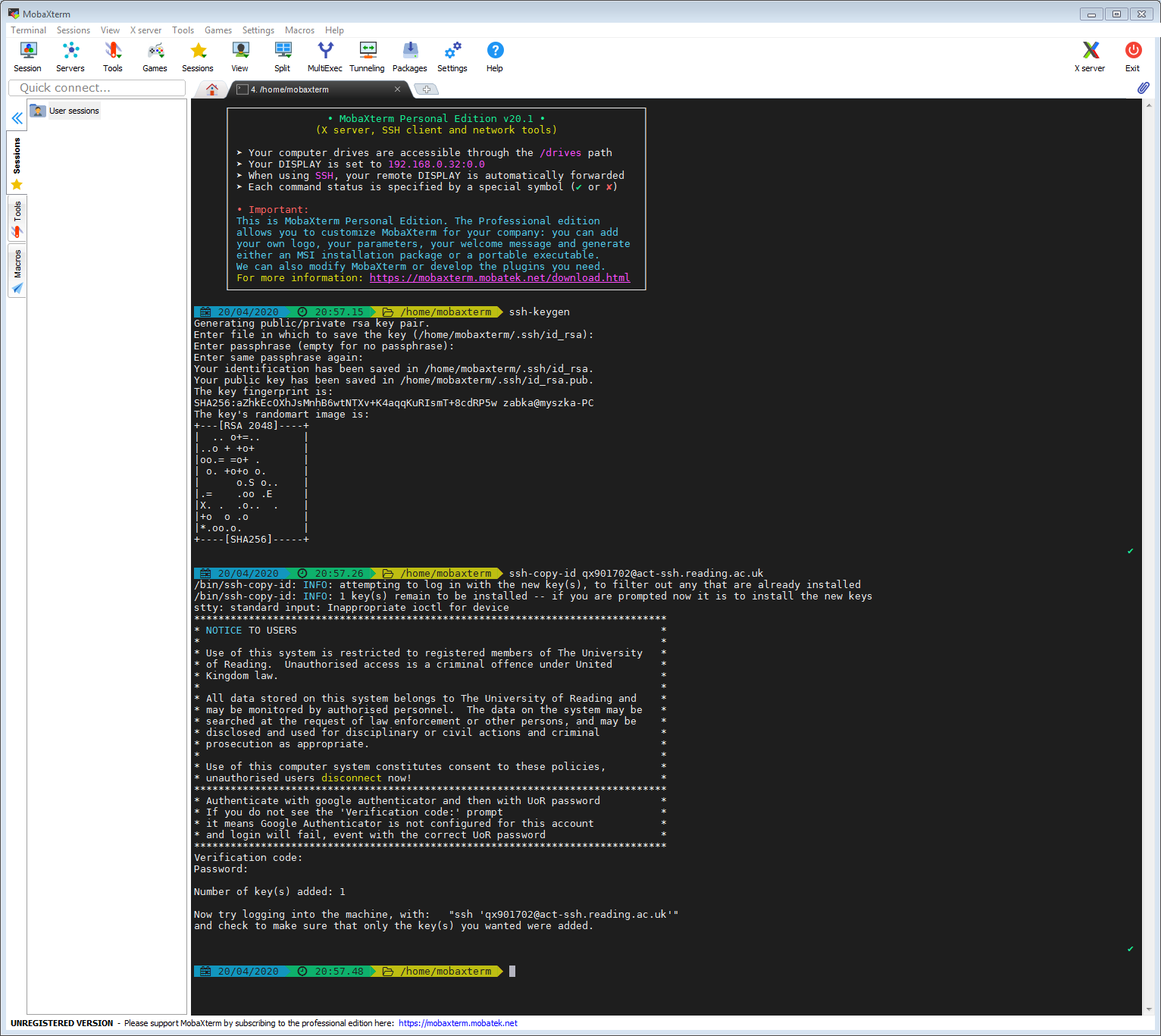 act-ssh with MobaXterm step step guide - Academic Computing Team
act-ssh with MobaXterm step step guide - Academic Computing Team
-
 Accessing a Remote via Authentication Blog
Accessing a Remote via Authentication Blog
-
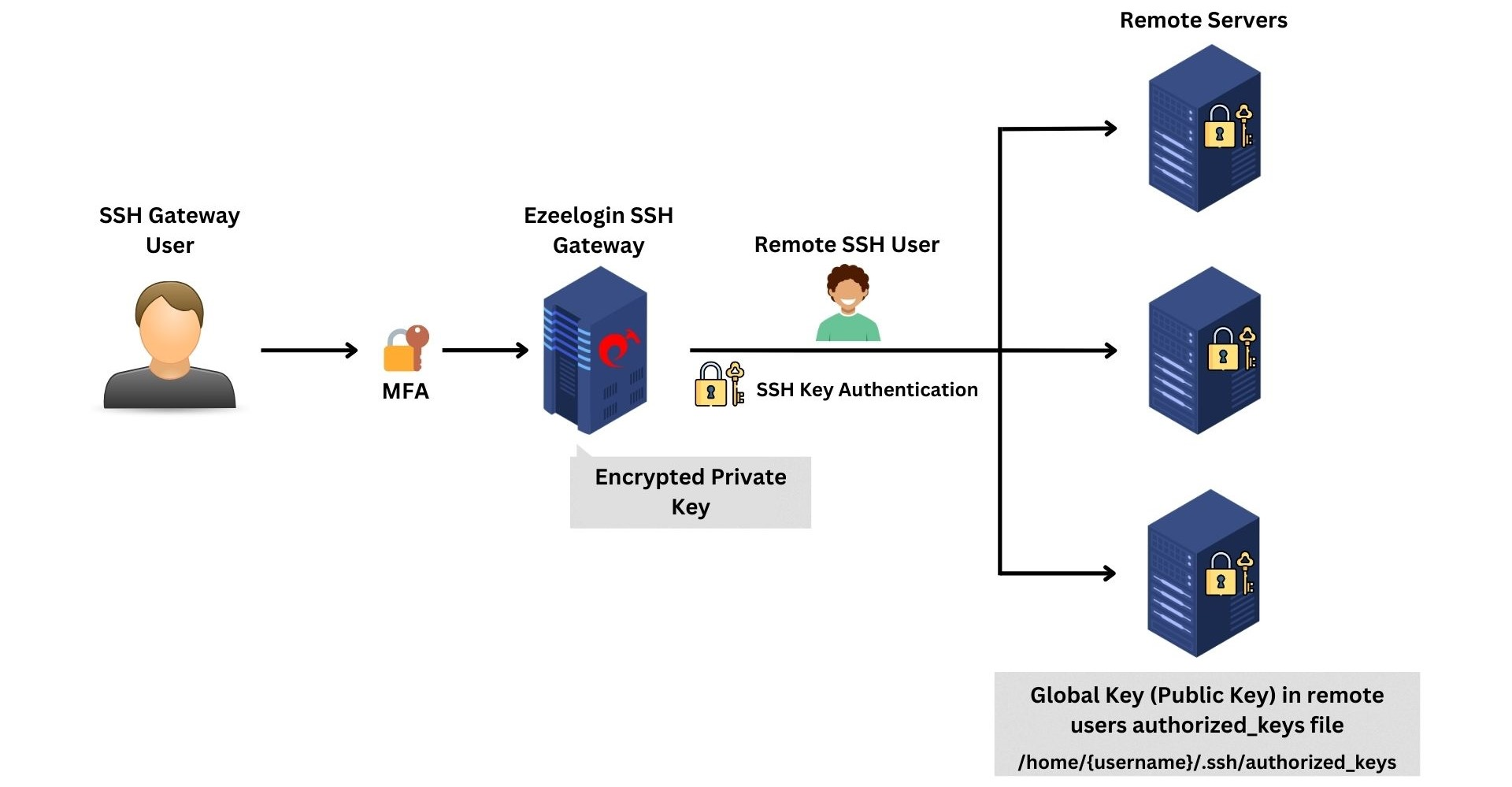
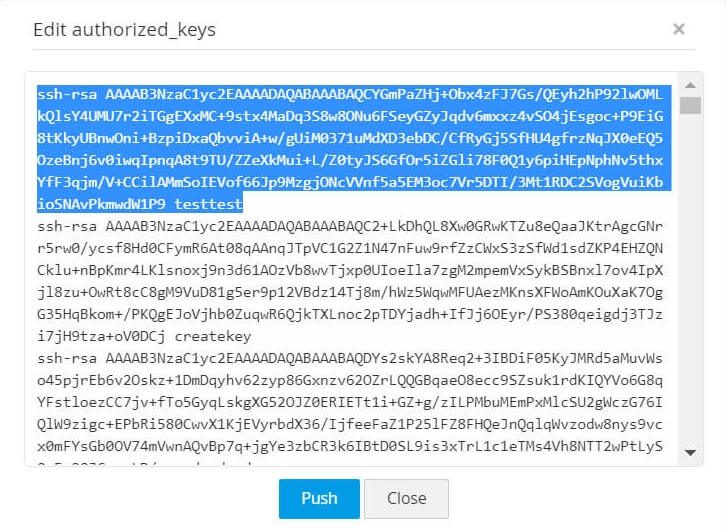 Manage SSH
Manage SSH
-
 keys explained DEV Community
keys explained DEV Community
-
 What is the Keys File SSH?
What is the Keys File SSH?
-
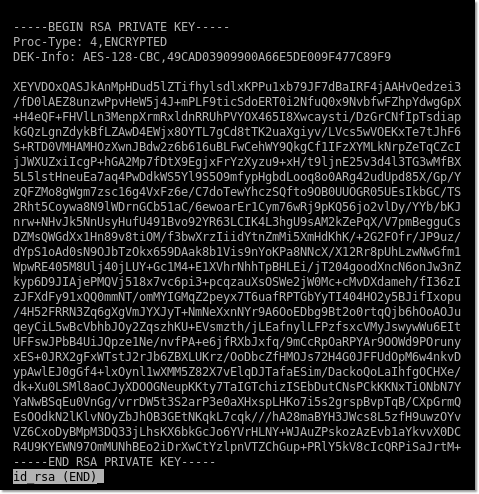
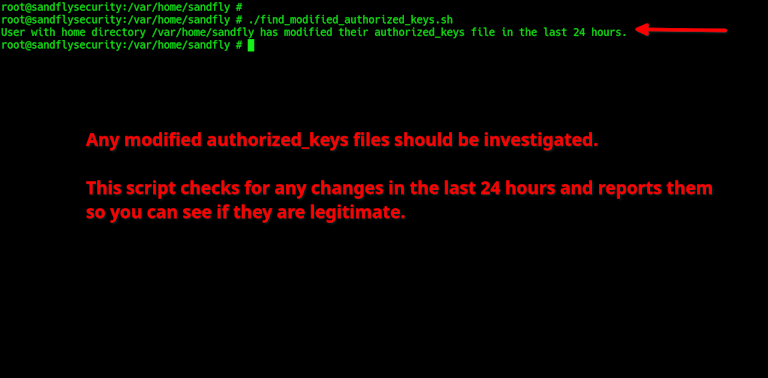 SSH Compromise Risks and
SSH Compromise Risks and
-
 Public Authentication With PuTTY
Public Authentication With PuTTY
-
 The Guide to Generating and SSH Keys - HostDime Base
The Guide to Generating and SSH Keys - HostDime Base
-
 Public Authentication With PuTTY
Public Authentication With PuTTY
-
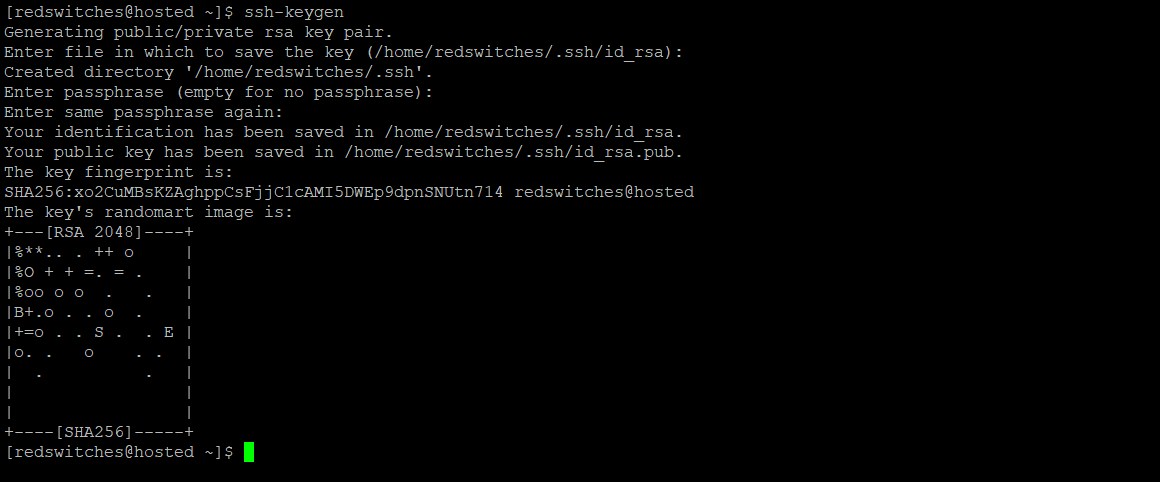 SSH For Server 4 Easy Steps
SSH For Server 4 Easy Steps
-
 SSH Key rotation to
SSH Key rotation to
-
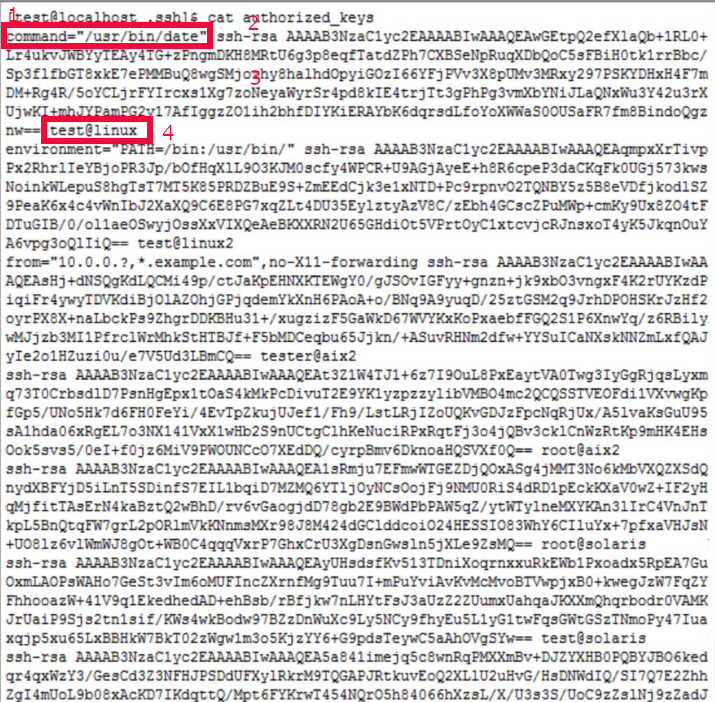 Restrict to Run one remote Server only via SSH authorized key passwordless authentication on / UNIX / BSD - ☩ Walking in Light with Christ - Faith, Computing, Diary
Restrict to Run one remote Server only via SSH authorized key passwordless authentication on / UNIX / BSD - ☩ Walking in Light with Christ - Faith, Computing, Diary
-
 How to use Key Linux | Average Linux User
How to use Key Linux | Average Linux User
-
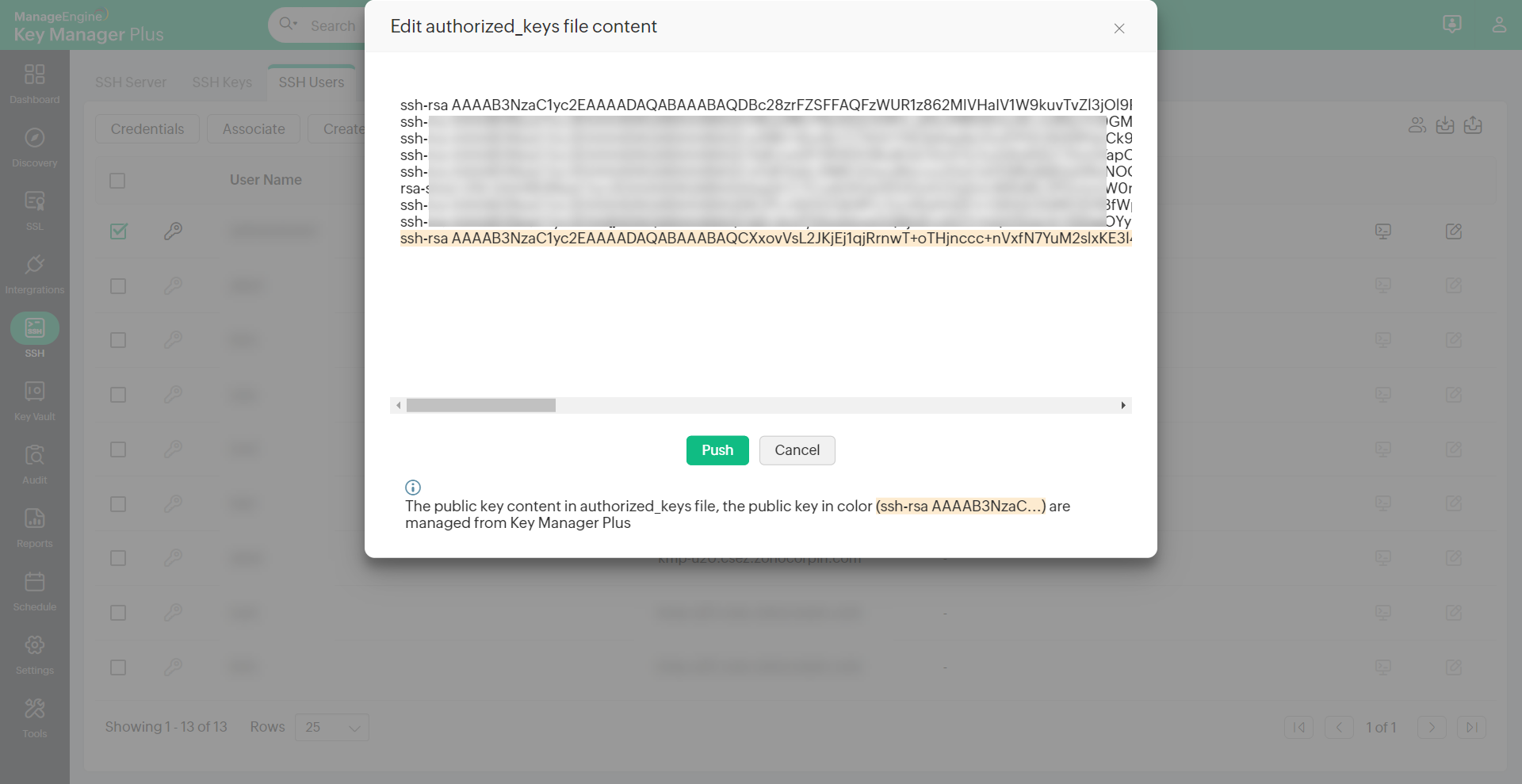 Manage SSH
Manage SSH